BlockThreat - Week 22, 2025
Cork Protocol | Malda | Dexodus | Kidnappings
Greetings!
More than $12M was stolen this week across six incidents. The largest loss came from the Cork Protocol exploit, which featured a kill chain involving at least three well-known vulnerability classes including insufficient function access control and reward manipulation. The remaining incidents followed a similar pattern of more access control failures and price oracle manipulation.
What’s becoming increasingly clear is that the same attack vectors keep resurfacing. These are not novel bugs. We should know them by now! So this week, I’m stepping back to highlight the Top 10 recurring attack vectors. Understanding these trends is essential to finally break the cycle of repeating the same mistakes.
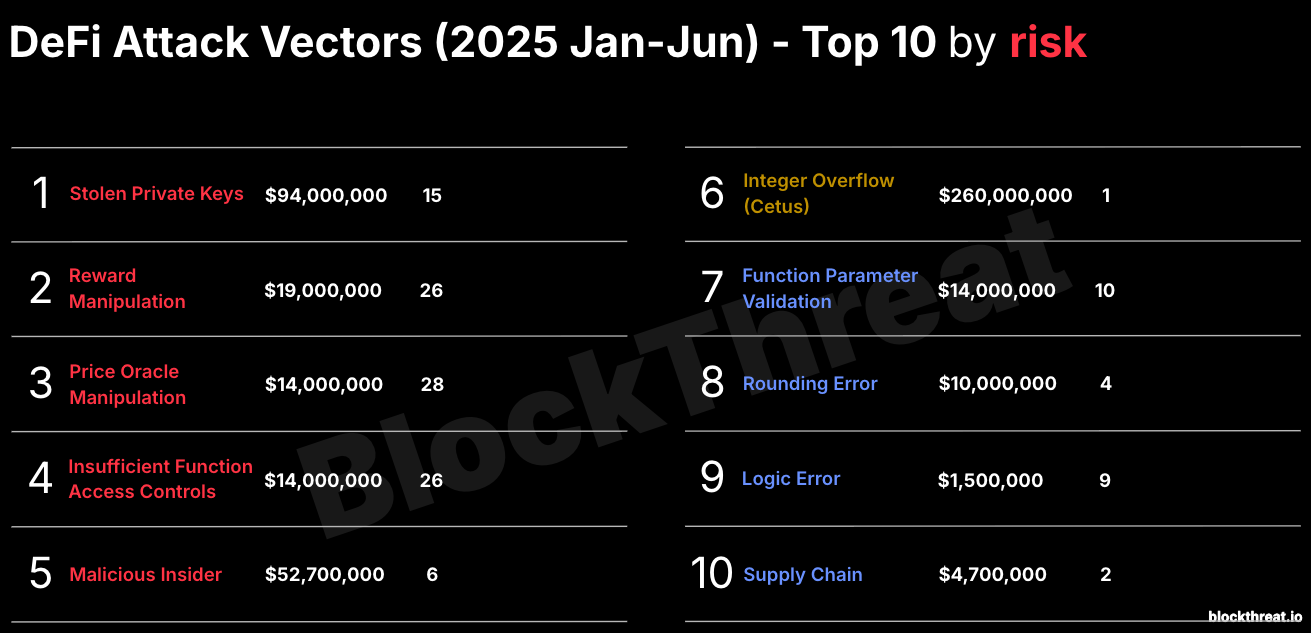
Stolen private keys continue to top the charts. Addressing these operational security failures requires more than traditional code audits. Unfortunately, a holistic approach—one that includes analysis of both on-chain and off-chain components like endpoint security, cloud infrastructure, and key management—is still far from standard practice.
More concerning, however, is the rise of a deadly triad: Reward Manipulation, Price Oracle Manipulation, and Insufficient Function Access Controls. These three attack classes show up in the majority of high-impact incidents including this week’s $12M Cork Protocol exploit.
Notably, Reward Manipulation has clawed its way back into the #3 spot after a relative decline over the past year. This vector targets flawed incentive mechanisms, allowing attackers to extract protocol rewards such as fees, yield, or emissions without providing corresponding economic value or taking on real risk.
To help catch this vulnerability class consider adopting the following audit/code review practices and study respective case studies.
- Verify that reward are proportional to economic contributions or risk (see Abracadabra Incident - $13M).
- Simulate accounting logic behavior in various edge cases (see Euler Hack - $197M).
- Trace every reward path and ensure that it can’t be manipulated (see Pickle Finance - $19.7M).
As in previous years, there’s always one standout hack that revives an attack vector we thought was mostly behind us. In 2025, it was Cetus on Sui that forced the industry to revisit the classic integer overflow—a bug class we haven't seen dominate in quite some time.
The rest of the Top 10 attack vectors remained largely consistent with prior years, with one notable exception: the appearance of the supply chain attack. This Web2-style operational security vector highlights the growing risks in our build and deployment pipelines. So please lock down your repos, audit your CI/CD workflows, and clean up your dependencies before attackers beat you to it.
Blockchain security demands staying constantly vigilant to emerging threats while prioritizing the most critical risks to address. I hope you will use the list above to build a safer and more resilient ecosystem.

Let’s dive into the news!
News
- FreeRomanStorm campaign needs donations to support the upcoming trial!
- Inside the $400 million Coinbase breach: An Indian call center and teenage hackers. More details are revealed about TaskUs call center and threat actors behind the attack. According to the recent filing the breach dates back to December 26, 2024, but was only discovered on May 11, 2024.
- Coinbase sued in class action over stock price drop tied to data breach reveal, alleging disclosure ‘omissions’.
- Banking groups urge SEC to rescind Biden-era cybersecurity rule.
- Someone loses over $500,000 in deUSD liquidation, raising concerns about Chainlink’s VWAP pricing system. Some debate ensued regarding the use of Chainlink oracles and low liquidity tokens. Time to check out Cyfrin’s excellent Chainlink Fundamentals course.
- Solana’s Raj Gokal doxxed via Migos’ Instagram account after failed 40 BTC extortion bid.
- Julia Garner and Anthony Boyle will portray Caroline Ellison and Sam Bankman-Fried in the new limited series The Altruists.
Crime
- France charges 25 suspects in crypto abduction cases. Hopefully, this marks the end of the recent string of kidnappings in France.
- Third Arrest Made in High-Profile Kidnapping of Bitcoin Investor in New York.
- Stolen Crypto Traced: Ugandan Police Arrest Suspect in Blockchain Educator’s Abduction.
- Russian national arrested in South Korea for attempted crypto robbery.
- Crypto Up, Kidnapping Up? — Dissecting Cases from 2022 to 2025.
- BitMEX thwarts supposed Lazarus attack, discovers group’s IP addresses and ‘significant lapses’ in security.
- North Korea likely got Lazarus to work days after warship fiasco.
- FBI Warns of Filipino Tech Company Running Sprawling Crypto Scams.
- Interpol target ‘Madam Ngo’ arrested over $300M crypto scam.
Phishing
- Infrastructure Used to Manage Domains Related to Cryptocurrency Investment Fraud Scams between October 2023 and April 2025 by FBI.
- Not your seed = not your keys, a new ongoing attack where you could lose everything by Opsek.
- Wintermute’s ‘CrimeEnjoyor’ to flag Ethereum’s wallet-draining contracts.
- Top 7702 Delegator Revealed as Phishing Scam by GoPlus Security.
- Dark Partner Hackers Using Fake AI, VPN & Crypto Sites to Attacks macOS & Windows Users.
Scams
- MEXC exchange detects 200% surge in fraudulent activity in Q1.
- Latam Insights: Milei Dissolves Libra’s Investigation, Colombian CBDC Comes out of Stealth.
- LONG READ: How John Karony went from visionary to convicted fraudster.
- Bubblemaps launches ‘Time Travel’ tool for insider activity, rug pulls.
Malware
- A Wolf in Sheep’s Clothing: Analysis of the Osiris Malicious Browser Extension by SlowMist.
- Dark Partners cybercrime gang fuels large-scale crypto heists.
- Inside a VenomRAT Malware Campaign by DomainTools.
- PumaBot: Novel Botnet Targeting IoT Surveillance Devices by Darktrace.
- Hackers Exploiting Craft CMS Vulnerability To Inject Crypto Miner Malware.
- New Self-Spreading Malware Infects Docker Containers to Mine Dero Cryptocurrency.
Media
- bountyhunt3rz - Episode 15 - milotruck.
- Ross Ulbricht's Speech at Bitcoin 2025. Ross received a $31.4M donation shortly after.
Contests
- RethMatch - An onchain tournament for bots, inspired by Pac-Man and Agar.io.
Research
- Enforcing Transaction Simulation Integrity: Pectra Edition by Bitfinding.
- The Bug That Was Missed - How fuzzing for preconditions can lead to high severity vulnerabilities by Nican0r (Recon)
- Riverguard: Mutation Rules for Finding Vulnerabilities by Sebastian and Thomas (Neodyme).
- The Custodial Stablecoin Rekt Test by Benjamin Samuels (Trail of Bits).
- Enterprise Crypto OpSec: A Comprehensive Guide for Companies by Three Sigma.
- A Hitchhiker's Guide to Advance Solana Program Security by Accelerated Curve.
- A deep dive into Axiom’s Halo2 circuits by Filipe Casal, Jim Miller, Fredrik Dahlgren, Joe Doyle, Tjaden Hess, Marc Ilunga (Trail of Bits).
- Beyond Smart Contracts: A Deep Dive into Blockchain Infrastructure Security Auditing by Smriti Verma (OpenZeppelin).
- Security Frameworks by SEAL - ENS Best Practices by Ghadi Mhawej (JustaLab)
- Awesome Audits Checklists by ABDul Rehman (TheTradMod).
- LLM-BSCVM: An LLM-Based Blockchain Smart Contract Vulnerability Management Framework.
- Exposing Go's Hidden Bugs: A Novel Concolic Framework.
- A Systematic Classification of Vulnerabilities in MoveEVM Smart Contracts (MWC).
- A theoretical basis for MEV.
Tools
- Sui Trace - Visualize token transfer patterns and track blockchain transactions with our advanced network graph.
Hacks
Dexodus
Date: May 26, 2025
Attack Vector: Price Oracle Manipulation
Impact: $291,000 (Recovered $291,000)
Chain: Base
References:
https://x.com/TenArmorAlert/status/1927182139130327246
https://x.com/DexodusFinance/status/1927049294458097858
https://x.com/DexodusFinance/status/1927323039361913077
https://blog.solidityscan.com/dexodus-finance-hack-analysis-d699135f575c
Recovery:
https://x.com/DexodusFinance/status/1927334137209278750
https://x.com/DexodusFinance/status/1927766736478040088
Exploit:
https://basescan.org/tx/0x6ffb494293fc5c32c5a6ab7dc3fff1fcc6e90fba9a6d6e486ba0a15ce518147e
LIFE Protocol
Date: May 26, 2025
Attack Vector: Price Oracle Manipulation
Impact: $51,000
Chain: BSC
References:
https://blog.solidityscan.com/li-fi-hack-analysis-521388128d22
Exploit:
https://bscscan.com/tx/0x487fb71e3d2574e747c67a45971ec3966d275d0069d4f9da6d43901401f8f3c0
https://github.com/SunWeb3Sec/DeFiHackLabs/blob/main/src/test/2025-04/Lifeprotocol_exp.sol
Position Exchange
Date: May 27, 2025
Attack Vector: Stolen Private Keys
Impact: $14,000
Chain: BSC
References:
https://x.com/TikkalaResearch/status/1927397305839202401
Exploit:
https://bscscan.com/tx/0x20d3e2b03e528d43184cae971a168845914793305672c0e8e3dc0264f2ee7a2d
Usual Money
Date: May 28, 2025
Attack Vector: Insufficient Function Access Control
Impact: $43,000
Chain: Ethereum
References:
https://x.com/TenArmorAlert/status/1927667834387054634
https://x.com/SlowMist_Team/status/1927627465717055574
https://x.com/usualmoney/status/1927615179291828607
https://x.com/TikkalaResearch/status/1928481328158396486
Exploit:
https://etherscan.io/tx/0x585d8be6a0b07ca2f94cfa1d7542f1a62b0d3af5fab7823cbcf69fb243f271f8
Cork Protocol
Date: May 28, 2025
Attack Vector: Insufficient Function Access Control
Impact: $12,000,000
Chain: Ethereum
References:
https://x.com/Corkprotocol/status/1927808041984086083
https://x.com/PeckShieldAlert/status/1927720760811856047
https://x.com/SlowMist_Team/status/1928100756156194955
https://x.com/hklst4r/status/1927755386557255717
https://x.com/philfog/status/1927704265423757321
https://rekt.news/cork-protocol-rekt
https://x.com/dedaub/status/1928456705169387987
https://www.certik.com/resources/blog/cork-protocol-incident-analysis
Exploit:
https://x.com/DecurityHQ/status/1929576443970806248
Malda (Mendi Finance)
Date: May 30, 2025
Attack Vector:
Impact: $281,000
Chain: Linea
References:
https://x.com/CyversAlerts/status/1928557133513228405
https://x.com/malda_xyz/status/1928545070052970928
https://x.com/QuillAudits_AI/status/1928649148082860167
Negotiations:
https://x.com/malda_xyz/status/1929981145065676942
Exploit:
https://lineascan.build/tx/0x7ffb4569827ed3acd595270c755195da5c630a1ad999afe6eb9b884ff09d6e5d

