BlockThreat - Week 18, 2025
Solana | Scroll | Kraken | DPRK | TeleMessage | Nomad

Greetings!
Just a few minor exploits this week, with net losses under $100K. Quiet weeks like these are rare—but they give us the space to explore broader trends in the industry.
One such trend is particularly concerning: two infinite mint vulnerabilities were recently patched by the Solana and Scroll chains. While blockchain-wide exploitation is rare, its potential impact is devastating. As more chains launch—some with completely novel consensus or transaction logic, others built on existing infrastructure but with unique quirks and precompiles—the likelihood of a blockchain-level exploit grows. We may be approaching a major hack rooted in this attack vector.
Now’s the time to give your audits and testing the extra attention they deserve—and take advantage of an exclusive discount from our repeat sponsor: Recon!
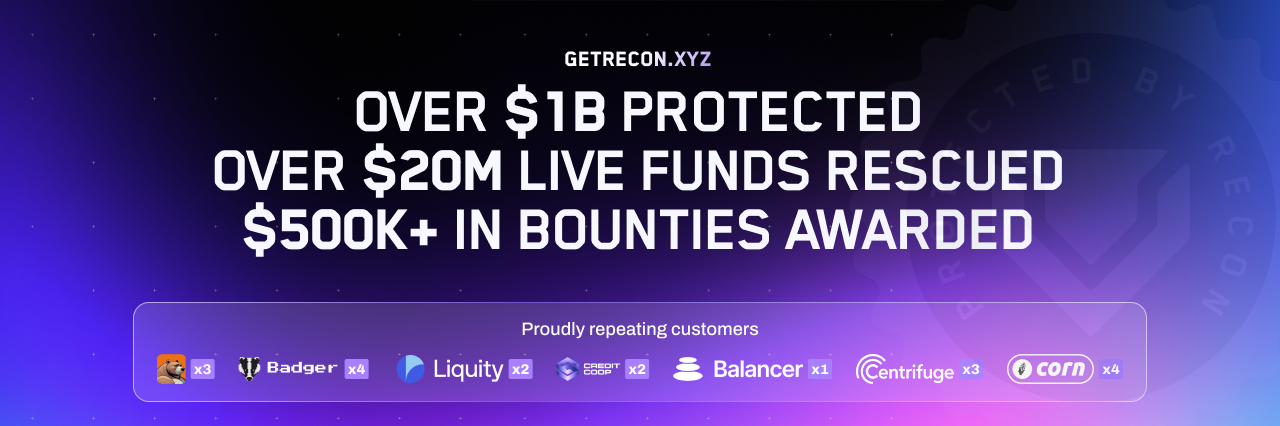
Get a Recon Invariant Audit: a powerful testing suite plus world-class auditors to catch what others miss. Open-source, no vendor lock-in, and proven to find severe bugs. Before spending millions on audits, invest in tests that evolve over time that catch bugs and keep them from coming back. Use promo code BLOCKTHREAT for a 5k discount on your first engagement.
See our portfolio: https://getrecon.xyz/blockthreat
Last week I attended BSides and RSA in San Francisco, and it highlighted a persistent cultural divide between the blockchain security community and traditional infosec. Just glance at the talk lineups—or chat with attendees—and the contrast is obvious.
RSA and BSides focus on infrastructure defense, SecOps, endpoint protection, threat modeling, compliance, and now AI. It's about protecting large organizations at scale. Meanwhile, at the DeFi Security Summit, we’re deep into smart contract exploits, MEV, on-chain forensics, and protocol-specific bugs. Both sides aim to protect assets—but the threat models, assumptions, and priorities couldn’t be more different.
This gap has real consequences. Many traditional security folks dismiss crypto as hype-ridden and scam-prone, not worth their time. And in crypto security, we sometimes overlook classic attack surfaces—infra misconfigs, phishing, repo security —because we’re focused on contracts and formal verification. That’s how we end up getting rekt by old-school TTPs, while the traditional world misses how fast threat actors are evolving on-chain. Just ask SEALs what they’re dealing with every week.
It’s time to bridge the gap. If you're in DeFi security, consider bringing your insights to DEF CON or Black Hat. If you're in traditional infosec, dig into DeFi post-mortems and bring your infra/opsec skills to a space that needs them badly. We're all fighting the same fight—it’s time to do it together.
And speaking of stepping outside the smart contract bubble, protect your people and operations with help from this week’s sponsor: Opsek.

Is your team safe from sophisticated threat actors?
More than 98% of stolen funds in the Web3 ecosystem are hacked without breaking code but by breaking people. Opsek will train your team to become paranoid, and harden your complete operational security stack.
You are already a target, don't get rekt.
Link: https://opsek.io/
Let’s dive into the news!
News
- Solana validators patch zero-day bug that could have led to unlimited minting of certain tokens.
- Scroll Mainnet Emergency Upgrade on 2025-04-25 by haichen (Scroll). One of the bugs could allow infinite mint of ETH and ERC20 tokens on the chain.
- The Signal Clone the Trump Admin Uses Was Hacked. If you have ever used TeleMessage to archive Signal, Telegram, WhatsApp, WeChat, SMS, etc. for any sensitive data consider it leaked.
- How we identified a North Korean hacker who tried to get a job at Kraken by Kraken. Be sure to check out the CBS interview.
- AirBorne: Wormable Zero-Click RCE in Apple AirPlay Puts Billions of Devices at Risk by Oligo Security.
- Pectra upgrade is coming on May 7, 2025. Here is an overview of what’s coming including EIP-7702 which will unlock new UX capabilities, but also new classes of phishing attacks.
- Wallet Security Ranking: Second Edition — April 2025 by Coinspect.
Crime
- Hacker behind $190m DeFi exploit from 2022 arrested in Israel. The Nomad Bridge exploit is one of the more unique hacks due to the sheer number of copycats jumping in on the protocol after the first exploit by the attacker.
- ZachXBT says $330 million bitcoin theft victim is an 'elderly' person in US - The Block.
- Abducted father of crypto-millionaire freed in French police raid.
- Mango Markets exploiter Avraham Eisenberg sentenced to four years for child porn offense.
- US DOJ requests 20-year sentence for Celsius founder Alex Mashinsky.
- US Treasury targets Cambodia’s Huione in proposed rule, citing links to North Korean hackers.
- eXch Remains Active Despite Shutdown: How the Bybit Hack-linked Exchange Continues to Enable Laundering of CSAM Funds by TRM.
- Grinex Emerges as Likely Garantex Rebrand by TRM.
Policy
- Crypto leaders urge Trump to end ‘lawless campaign’ criminalizing software developers, including Roman Storm.
- SEC ends investigation into PayPal’s PYUSD stablecoin without enforcement.
- UK Government Targets Exchanges and Stablecoins With New Draft Crypto Rules.
Phishing
- Contagious Interview (DPRK) Launches a New Campaign Creating Three Front Companies to Deliver a Trio of Malware: BeaverTail, InvisibleFerret, and OtterCookie by Silent Push.
- TRON’s X account hacked in the latest social engineering attack.
- Ledger scammers are sending letters to steal your recovery phase.
- Google subpoena scam: What it looks like and how to avoid it.
Scams
- Blockchain Slumlords by Rekt.
Malware
- TerraStealerV2 and TerraLogger: Golden Chickens' New Malware Families Discovered by Insikt Group. The malware targets browser credentials, crypto keys, and other sensitive data.
Media
- OpenSense - An Auditor's Journey With Chris and Zokyo.
- Secureum - Fuzzing for Security Researchers with Alex The Entreprenerd.
- Around The Coin - Can Web3 Security End Crypto Hacks - Mitchell Amador.
- Ethereum Engineering - ByBit Hack Deep Dive by AYC.
Research
- Scroll Chain DoS via CCC Overflows in Single User Transactions by Shabarkin Security.
- The Hidden Risks of Cosmos: Unmetered Functions by Eduard Kotysh and Christian Vari (Oak Security).
- TON Security Primer: Part 1 by Gunhee (Zellic).
- SoK: A Survey of Mixing Techniques and Mixers for Cryptocurrencies.
- A Comprehensive Study of Exploitable Patterns in Smart Contracts: From Vulnerability to Defense.
- CodeBC: A More Secure Large Language Model for Smart Contract Code Generation in Blockchain.
- Real AI Agents with Fake Memories: Fatal Context Manipulation Attacks on Web3 Agents.
- Yield Tokenization Protocols, How They're Made: Pendle by Sergey Boogerwooger, Pavel Morozov (MixBytes).
Hacks
Unkn_OG
Date: April 28, 2025
Attack Vector: Social Engineering
Impact: $330,700,000 (Recovered $7,000,000)
Chain: Bitcoin
References:
https://x.com/zachxbt/status/1916756932763046273
Altura
Date: April 28, 2025
Attack Vector: Insufficient Function Access Control
Impact: $31,000
Chain: Ethereum
References:
https://x.com/TikkalaResearch/status/1916918809799393342
Exploit:
https://etherscan.io/tx/0x6086dc19843148c1d85939dec6aac832ad76644a1cf7b7a943c18e561cc54921
Unkn_c53a7e
Date: May 03, 2025
Attack Vector: Function Parameter Validation
Impact: $20,000
Chain: BSC
References:
https://x.com/TikkalaResearch/status/1918857517893030399
Exploit:
https://bscscan.com/tx/0x6a1c26f52a34c4507ea7722ccde298087f7cacbd22b22566f4c5c6ca9f9facc7
MHT Trade
Date: May 04, 2025
Attack Vector: Reward Manipulation
Impact: $25,000
Chain: BSC
References:
https://x.com/TikkalaResearch/status/1919071920877609271
Exploit:
https://bscscan.com/tx/0x8dd331f85aa87c47b01ee6a2884df35833d78a2715effe0582fa20b0ea981008

